Mail Access Monitor for CommuniGate Pro 3.9c
Free Trial Version
Publisher Description
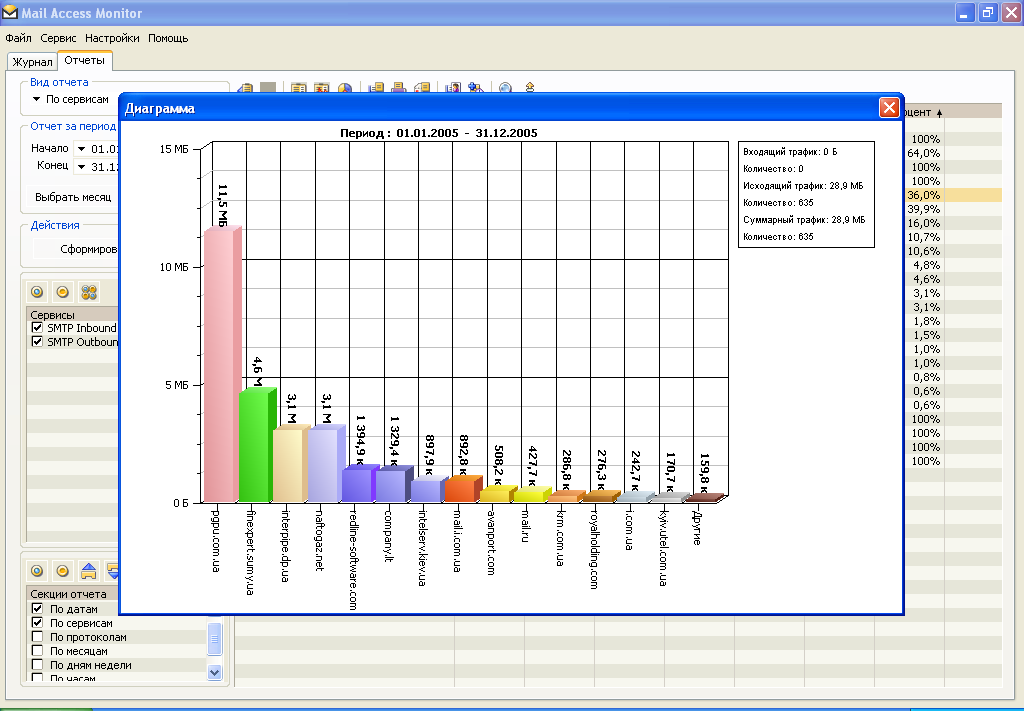
It is hard to imagine an office without access to e-mail. Just as hard as finding a large company that does not have irresponsible employees who prefer exchanging e-mail messages with their friends rather than doing their job. If you are a manager, business owner or IT specialist, you have to know that there is a simple, quick and inexpensive way to take control of corporate e-mail system. Mail Access Monitor is a simple tool that analyses mail server logs and shows how much traffic is being used by e-mail, who sends and receives most messages, where the messages are being send to and if e-mail abuse takes place in your office. The program works with all popular e-mail servers (MDaemon, Kerio MailServer, Merak Mail Server, MS Exchange Server, VisNetic MailServer, SendMail, PostFix, CommuniGate Pro and QMail) and builds charts that are easy to comprehend. A simple glance at the chart reveals a lot of information. For example, you may find out that most outgoing e-mail messages are not related to work in any way and cost you hundreds of dollars in extra traffic a year. Or that some employees average 30-50 emails a day. Or, on the other hand, some of your sales staff members who are supposed to be proactive at approaching clients only reply to incoming messages. The best part of Mail Access Monitor is that it starts working right after installation (which takes less then 1 minute) and frees you from having to look over employees shoulders. As soon as employees learn that their e-mail use is being tracked and that the abusers will be punished, their productivity increases drastically. In fact, Mail Access Monitor is so effective that some Fortune 500 companies made it a mandatory policy to have the program installed in every office and branch around the globe! To see how Mail Access Monitor can help your company fight e-mail abuse, download free trial version now!
About Mail Access Monitor for CommuniGate Pro
Mail Access Monitor for CommuniGate Pro is a free trial software published in the Network Monitoring list of programs, part of Network & Internet.
This Network Monitoring program is available in English, French, German, Italian, Russian, Spanish. It was last updated on 22 April, 2024. Mail Access Monitor for CommuniGate Pro is compatible with the following operating systems: Windows.
The company that develops Mail Access Monitor for CommuniGate Pro is Red Line Software. The latest version released by its developer is 3.9c. This version was rated by 1 users of our site and has an average rating of 4.0.
The download we have available for Mail Access Monitor for CommuniGate Pro has a file size of 5.24 MB. Just click the green Download button above to start the downloading process. The program is listed on our website since 2011-02-14 and was downloaded 104 times. We have already checked if the download link is safe, however for your own protection we recommend that you scan the downloaded software with your antivirus. Your antivirus may detect the Mail Access Monitor for CommuniGate Pro as malware if the download link is broken.
How to install Mail Access Monitor for CommuniGate Pro on your Windows device:
- Click on the Download button on our website. This will start the download from the website of the developer.
- Once the Mail Access Monitor for CommuniGate Pro is downloaded click on it to start the setup process (assuming you are on a desktop computer).
- When the installation is finished you should be able to see and run the program.